Team Response After the Incident
What a team does in the hours, days, and weeks after a major security incident tells you everything about their character. Here is the documented record.
Official Acknowledgment — January 28, 2022
Section titled “Official Acknowledgment — January 28, 2022”The Qubit Finance team posted to Twitter acknowledging the hack:
“The protocol was exploited by; 0xd01ae1a708614948b2b5e0b7ab5be6afa01325c7. The hacker minted unlimited xETH to borrow on BSC. The team is currently working with security and network partners on next steps. We will share further updates when available.” — @QubitFin, 9:14 AM, January 28, 2022

BSCScan: The Exploit Transactions
Section titled “BSCScan: The Exploit Transactions”The hacker’s transactions — labeled “QubitFin Exploiter” by BSCScan — show repeated Borrow calls in rapid succession on the same day:
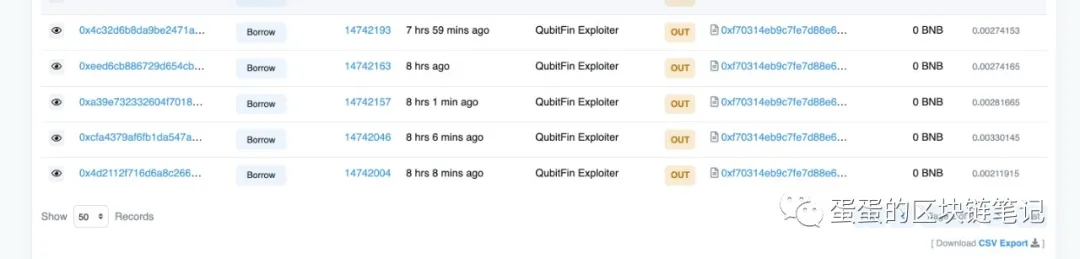
Key transactions visible:
0x4c32d6b8...— Borrow, Block 147421930xeed8cb88...— Borrow, Block 147421630xa39e7323...— Borrow, Block 147421570xcfa4379a...— Borrow, Block 147420460x4d2112f7...— Borrow, Block 14742004
All directed to the same contract: 0xf70314eb9c7fe7d88e6...
What the Team Did
Section titled “What the Team Did”Offered the hacker $250,000 to return $80M
Section titled “Offered the hacker $250,000 to return $80M”The team’s public response was to offer the attacker a “bug bounty” of $250,000 — asking them to keep $250K and return the remaining $79.75M. The hacker did not respond.
Claimed to file police reports (unverified)
Section titled “Claimed to file police reports (unverified)”The team stated they reported the hack to police in two jurisdictions. No case numbers, no filing confirmations, and no law enforcement updates have ever been provided publicly.
Sent @moleh to manage victims
Section titled “Sent @moleh to manage victims”The team deployed one representative — moderator @moleh — to handle victim communications.
What the Team Failed to Do
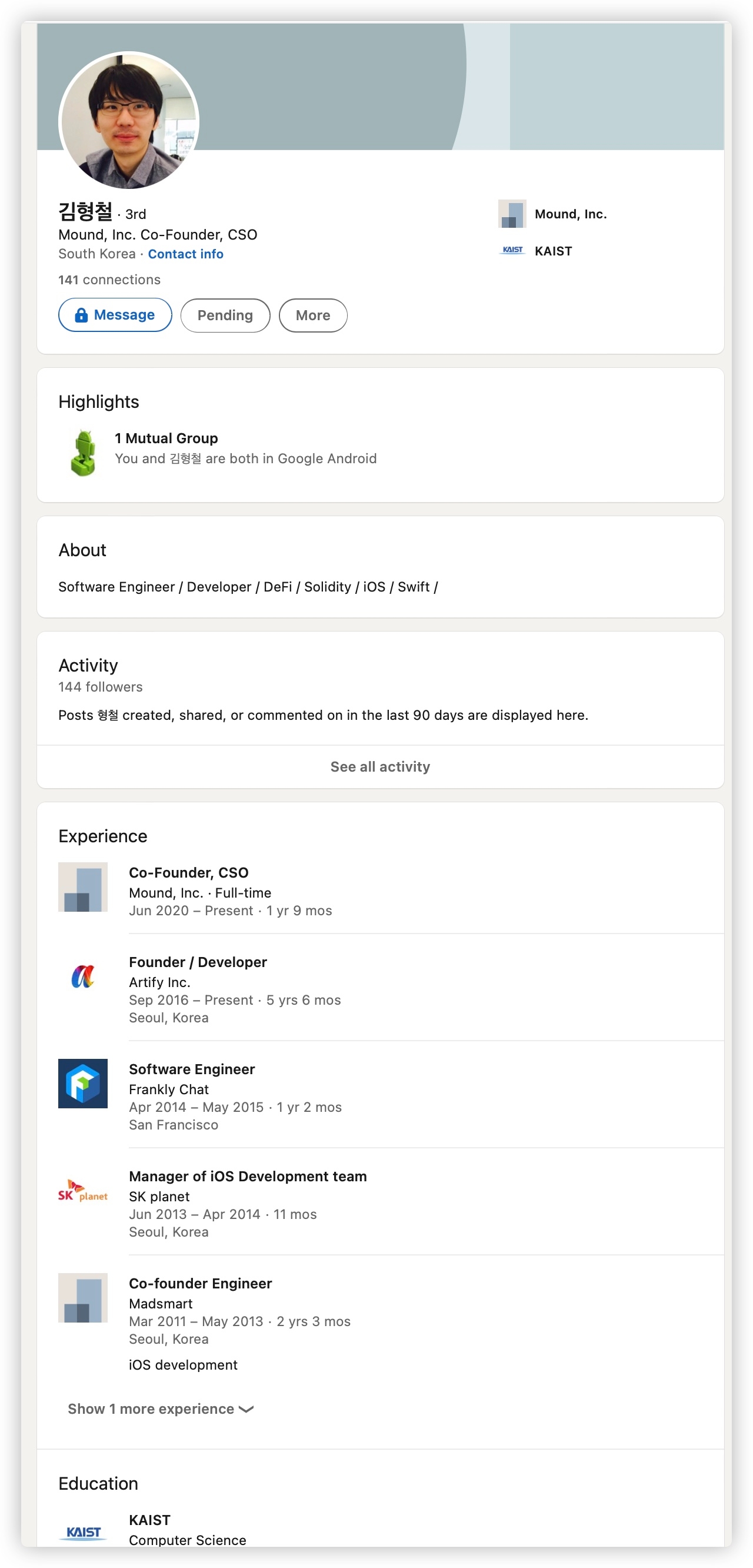
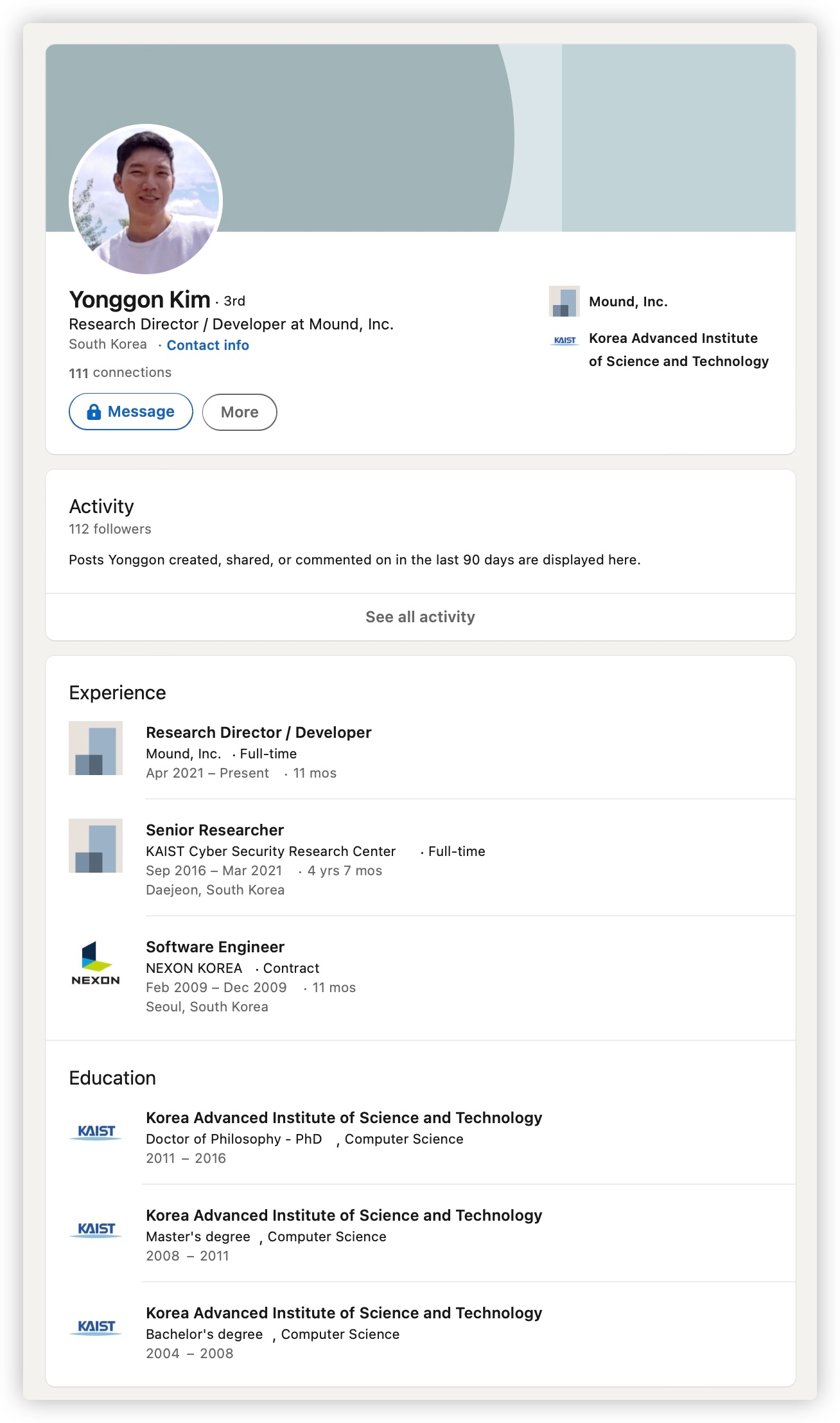
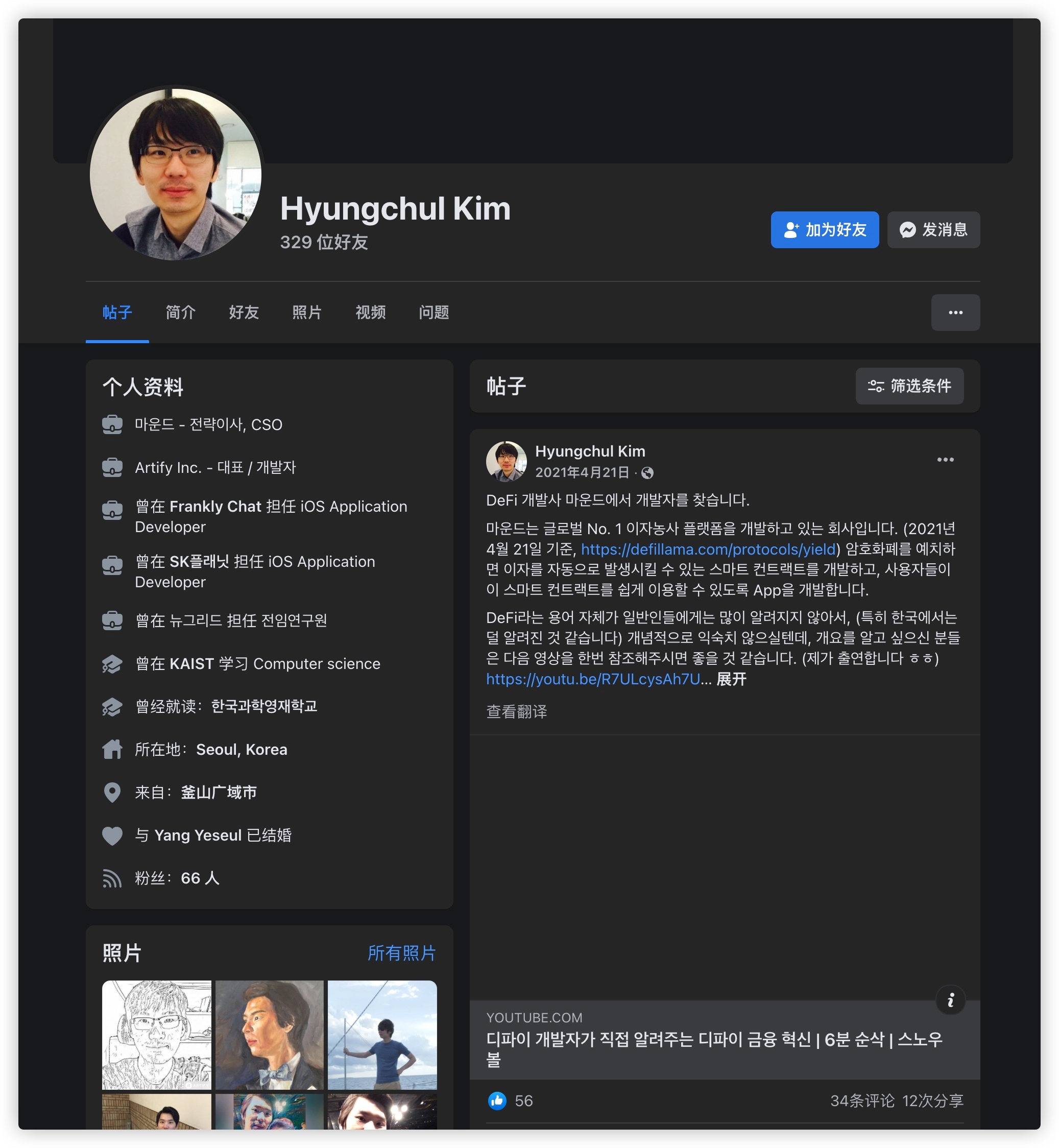
Section titled “What the Team Failed to Do”✗ CTO deleted LinkedIn — February 1, 2022
Section titled “✗ CTO deleted LinkedIn — February 1, 2022”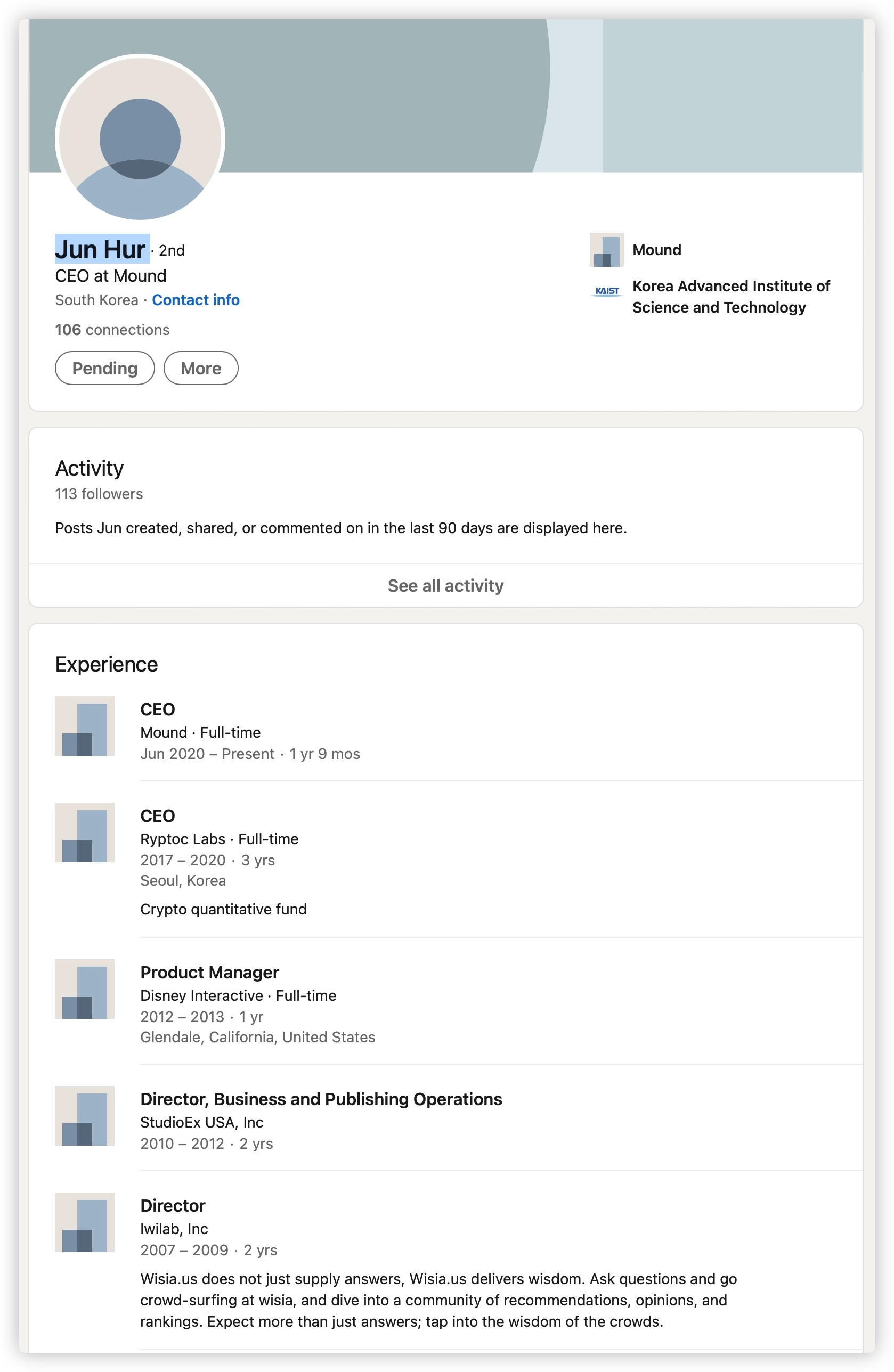
Four days after the hack, CTO Aaron Yooshin Kim deleted his LinkedIn profile (linkedin.com/in/aaromkimys). The community noticed and documented it immediately.
✗ Victims removed from official Telegram
Section titled “✗ Victims removed from official Telegram”The moderator @moleh systematically removed victims from the official Telegram group. Rather than keeping communication channels open for the people who had lost their savings, the team silenced them.
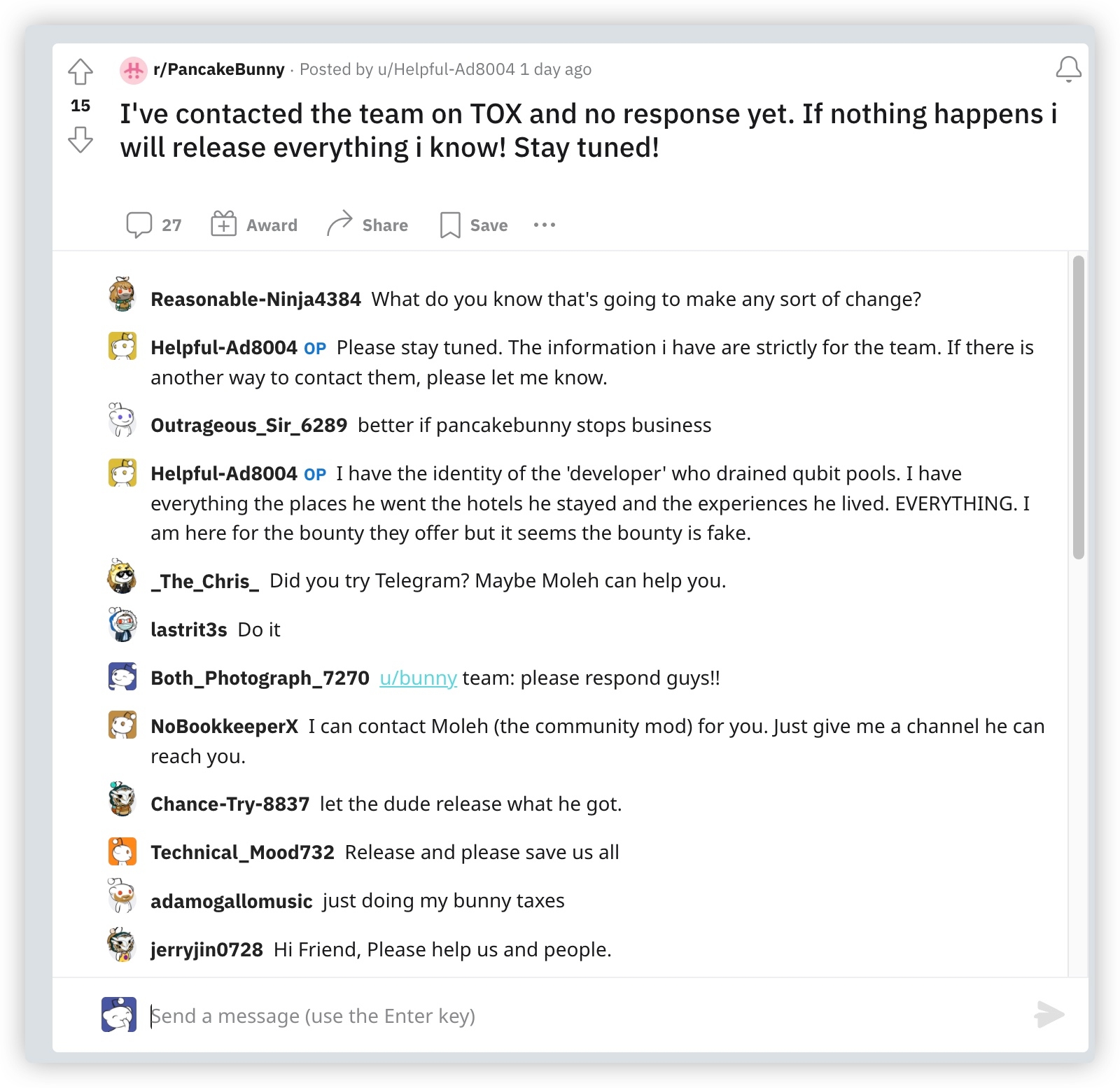
✗ No response to community members with hacker information
Section titled “✗ No response to community members with hacker information”A Reddit user posted they had contacted the team with information about the hacker’s identity — and received no response:
“I have the identity of the ‘developer’ who drained qubit pools. I have everything — the places he went, the hotels he stayed and the experiences he lived. EVERYTHING. I am here for the bounty they offer but it seems the bounty is fake.” — u/Helpful-Ad8004, r/PancakeBunny
✗ Did not contact Binance or major exchanges to blacklist the hacker
Section titled “✗ Did not contact Binance or major exchanges to blacklist the hacker”No prompt action was taken to blacklist 0xd01ae1a708614948b2b5e0b7ab5be6afa01325c7 across exchanges, bridges, and swap protocols — standard practice after a DeFi exploit.
✗ Did not respond to people who came forward
Section titled “✗ Did not respond to people who came forward”Despite publicly asking for community help to identify the hacker, the team went silent when members reached out via Tox and other channels.
February 6–7, 2022 — Continued Silence
Section titled “February 6–7, 2022 — Continued Silence”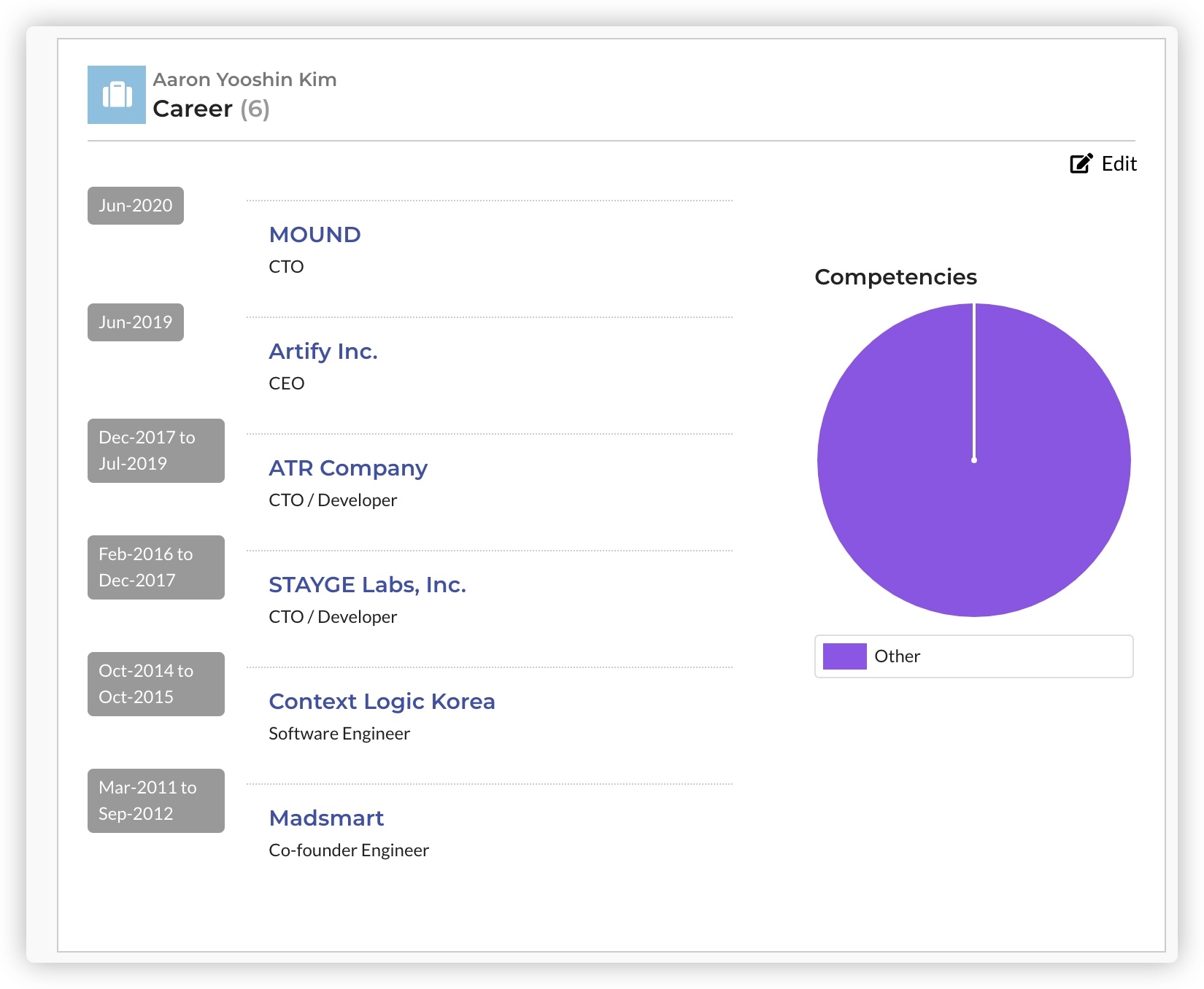
Binance’s Role
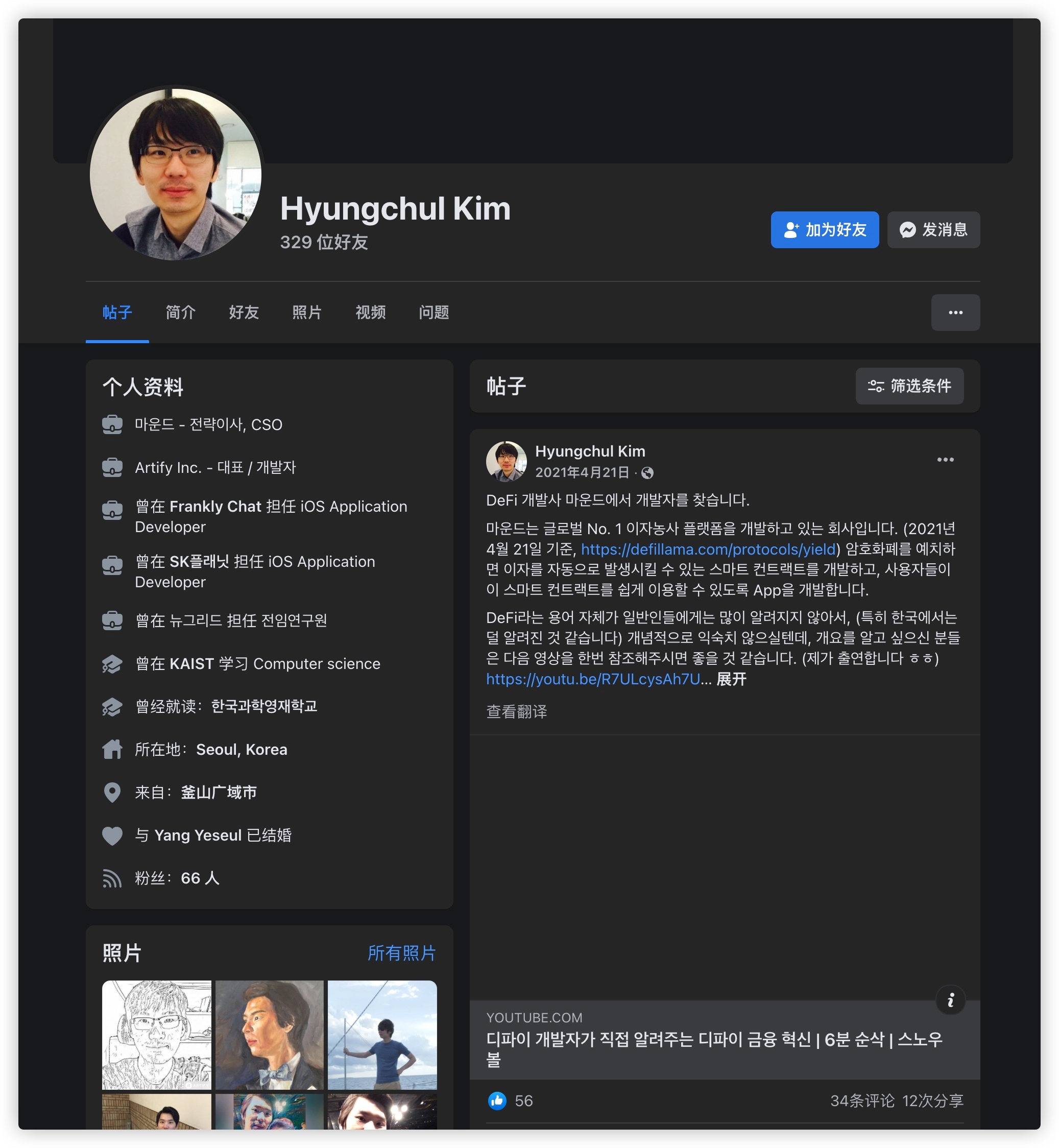
Section titled “Binance’s Role”Qubit Finance was a Binance-endorsed project and Mound Inc. received $1.6M from Binance Labs in April 2021. When victims appealed to Binance and CZ for help — to blacklist the hacker’s wallet, to apply pressure — they were ignored.
Four Years Later
Section titled “Four Years Later”As of 2026:
- Mound Inc.’s website (mound.finance) is offline
- No public updates from the team
- No compensation mechanism established
- No funds returned
- The victims are still waiting