CTO: Aaron Yooshin Kim (김유신)
Aaron Yooshin Kim (김유신) was the Chief Technology Officer and Co-Founder of Mound Inc. He held 20% of Krypton PTE. LTD. — the Singapore entity that controls Mound Labs. As CTO, he had direct technical responsibility for the QBridge architecture that was exploited for $80M.
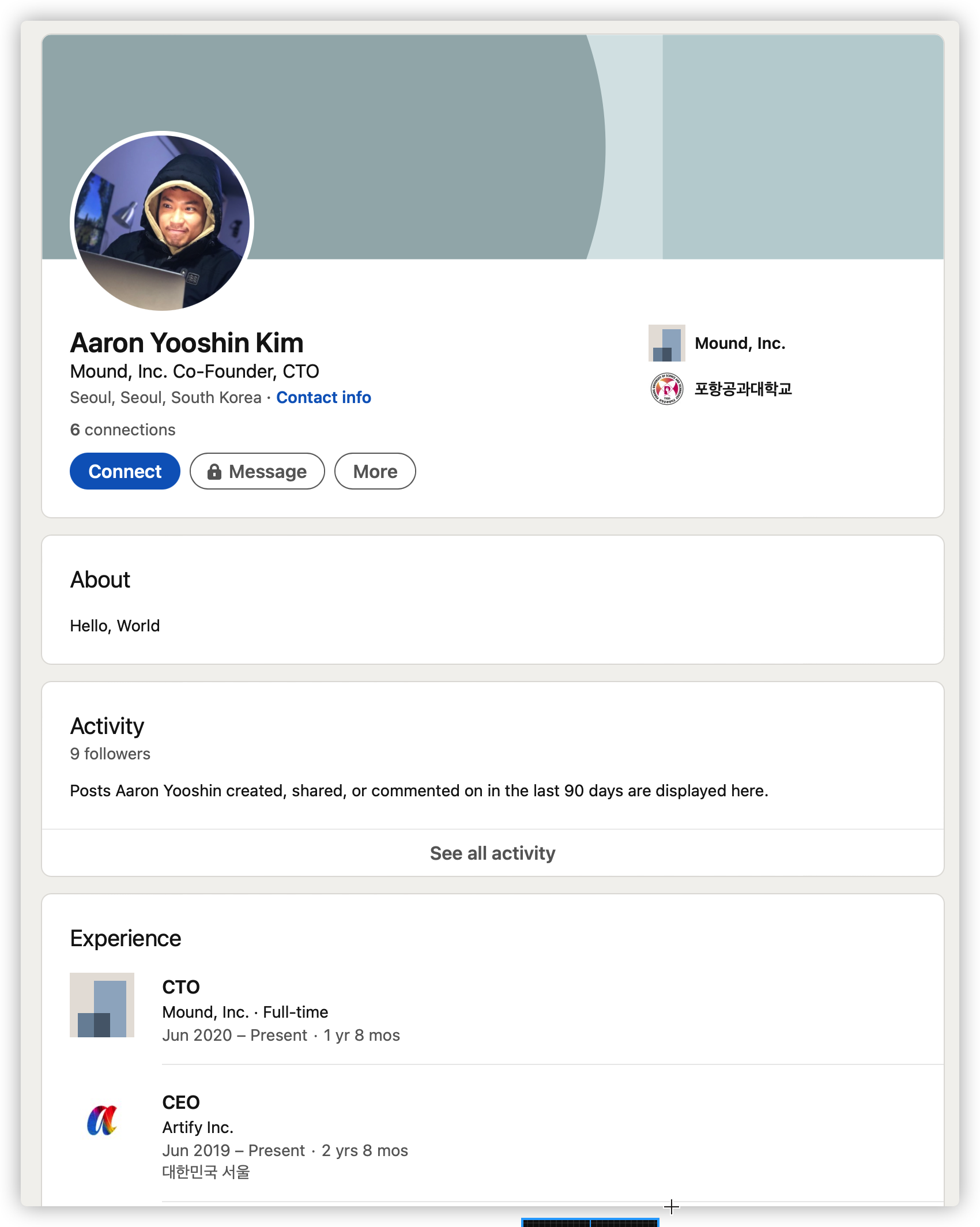
On February 1, 2022 — four days after the hack — Aaron Yooshin Kim deleted his LinkedIn profile.
Career History
Section titled “Career History”The following was captured from his LinkedIn (now deleted) and from TopioNetworks before deletion:
| Period | Company | Role |
|---|---|---|
| Jun 2020 – Present | Mound, Inc. | CTO (Co-Founder) |
| Jun 2019 – Present | Artify Inc. | CEO |
| Dec 2017 – Jul 2019 | ATR Company | CTO / Developer |
| Feb 2016 – Dec 2017 | STAYGE Labs, Inc. | CTO / Developer |
| Oct 2014 – Oct 2015 | Context Logic Korea | Software Engineer |
| Mar 2011 – Sep 2012 | Madsmart | Co-founder Engineer |
Education
Section titled “Education”| Institution | Credential |
|---|---|
| Pohang University of Science and Technology (POSTECH) | Bachelor of Science, Computer Science (2017) |
The LinkedIn Deletion
Section titled “The LinkedIn Deletion”The community noticed and documented the deletion on Reddit:
“News Alert — Aaron Yooshin Kim have deleted LinkedIn” — Reddit, r/PancakeBunny
- Deleted URL:
https://www.linkedin.com/in/aaromkimys - Date of deletion: February 1, 2022
- Days since hack: 4
No explanation was given. The profile had 6 connections and 9 followers at time of deletion. The LinkedIn profile showed he had been CTO since June 2020 — the same month Mound was founded.
Other Profiles
Section titled “Other Profiles”- Facebook: facebook.com/aak.artify
- TopioNetworks: Previously listed
Registered Address
Section titled “Registered Address”Per Krypton PTE. LTD. corporate filings:
103-dong 1003-ho, 391, Hyoryeong, Seocho-gu, Seoul, Korea
Technical Responsibility
Section titled “Technical Responsibility”As CTO, Aaron Yooshin Kim was directly responsible for:
- The architecture of QBridge and the QBridgeHandler smart contracts
- The decision to deploy the bridge without completing its security audit
- The
resourceIDparameter reassignment to the zero address — the precise change that enabled the exploit — which only the contract owner could make - Failure to account for the known EVM behavior (silent success on EOA calls) documented since 2019
Deleting one’s LinkedIn profile four days after losing $80M of user funds is not the behavior of someone planning to resolve the situation.